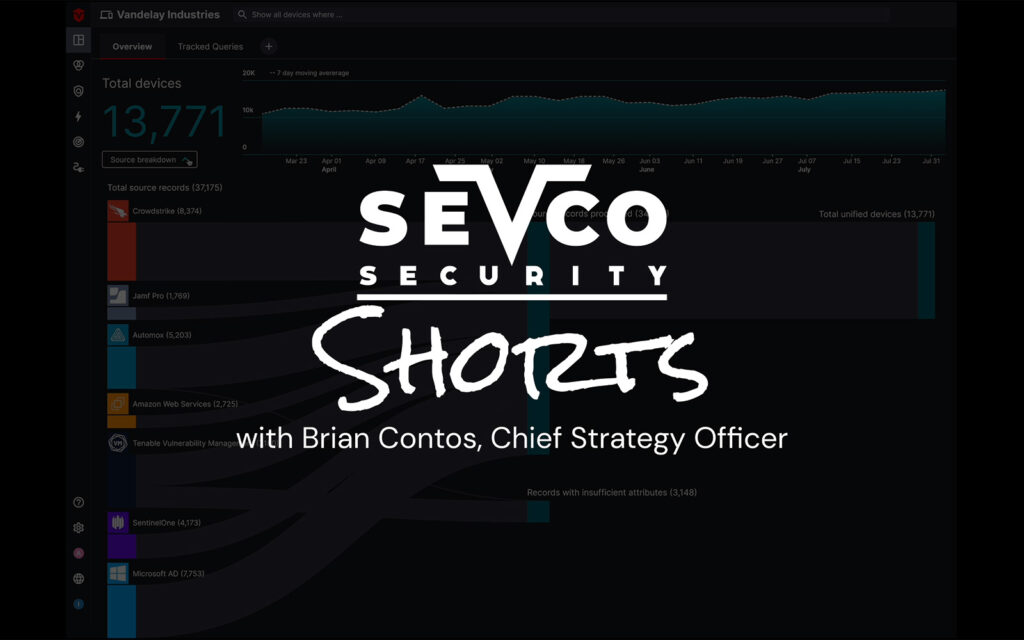
Sevco Security Shorts: Vulnerability and Exposure Management
Surface environmental vulnerabilities like missing agents and CVEs in one place to drive comprehensive prioritization and remediation.
Sevco Security Shorts: Vulnerability and Exposure Management Read More »