How Sevco Supports Continuous Threat Exposure Management (CTEM) Programs
Cybersecurity continues to evolve at a rapid pace, and with it comes the need for a more robust approach to managing risk across an ever-expanding attack surface. Continuous Threat Exposure Management (CTEM) is at the forefront of this evolution, offering organizations the ability to continuously identify, assess, prioritize, validate, and remediate risks across all assets. Many organizations are turning to an Exposure Assessment Platform (EAP) to help drive these programs.
We’ll explore CTEM, its five foundational pillars, and the EAP technology that supports its implementation. We’ll introduce Sevco and explain how our Exposure Assessment Platform enables organizations to implement and manage their own exposure management programs with all the intelligence they require from a single platform.
An Introduction to CTEM
The Challenge: Everchanging Data = Everchanging Risk
Organizations face a daunting challenge: how to reduce cyber risk in everchanging IT environments while simultaneously managing the increasing volume of exposures and vulnerabilities across the growing attack surface. Traditional approaches like vulnerability management and periodic assessments are no longer sufficient to address the dynamic threat landscape.
The continuously shifting nature of IT assets—new devices, users, configurations, vulnerabilities, and cloud deployments—means that the risks are perpetually evolving. Static, point-in-time assessments fail to keep pace with this flux.
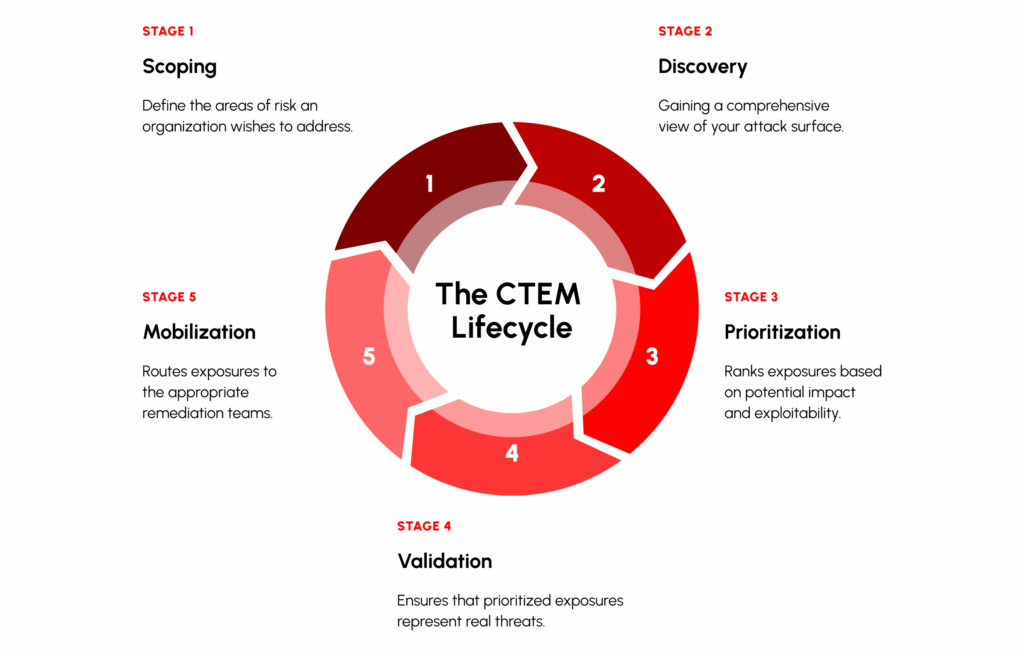
The Five Stages of CTEM
CTEM programs help organizations to address these challenges with five pillars:
- Scoping – Defining the organization’s assets and threat landscape.
- Discovery – Identifying vulnerabilities and misconfigurations across the environment.
- Prioritization – Assessing and ranking risks based on potential impact.
- Validation – Simulating and testing threats to confirm real-world exposure.
- Mobilization – Implementing remediation actions and monitoring improvements
How Do EAPs Support CTEM?
Exposure Assessment Platforms (EAPs) provide a centralized, integrated solution to manage exposures. By consolidating data from across diverse toolsets, EAPs offer real-time insights into an organization’s vulnerabilities and risk posture.
Effective CTEM relies on technology that:
- Provides comprehensive asset visibility
- Prioritizes vulnerabilities based on technical and business context alongside threat intelligence
- Validates risks with real-world simulations
- Mobilizes remediation efforts efficiently and collaboratively
The Sevco Exposure Assessment Platform (EAP)
Sevco helps organizations who have too many issues to address, and too little intelligence on which exposures and vulnerabilities present the greatest risk.
The Sevco EAP consolidates comprehensive intelligence needed to more effectively prioritize vulnerabilities for remediation in a single platform. We built flexible, powerful prioritization capabilities and uniquely centralized the greatest risks of all types – CVEs, missing agents, business-critical assets missing security controls – into a single dashboard, prioritized by risk.
Sevco is a complete Exposure Assessment Platform, empowering organizations to operationalize their CTEM programs effectively.
Cyber Asset Attack Surface Management / Inventory: CTEM Scoping
Many organizations struggle with incomplete and inaccurate asset inventories. Many solutions try to solve this problem, but their inventories continue to fall short, resulting in security gaps and leaving exposures.
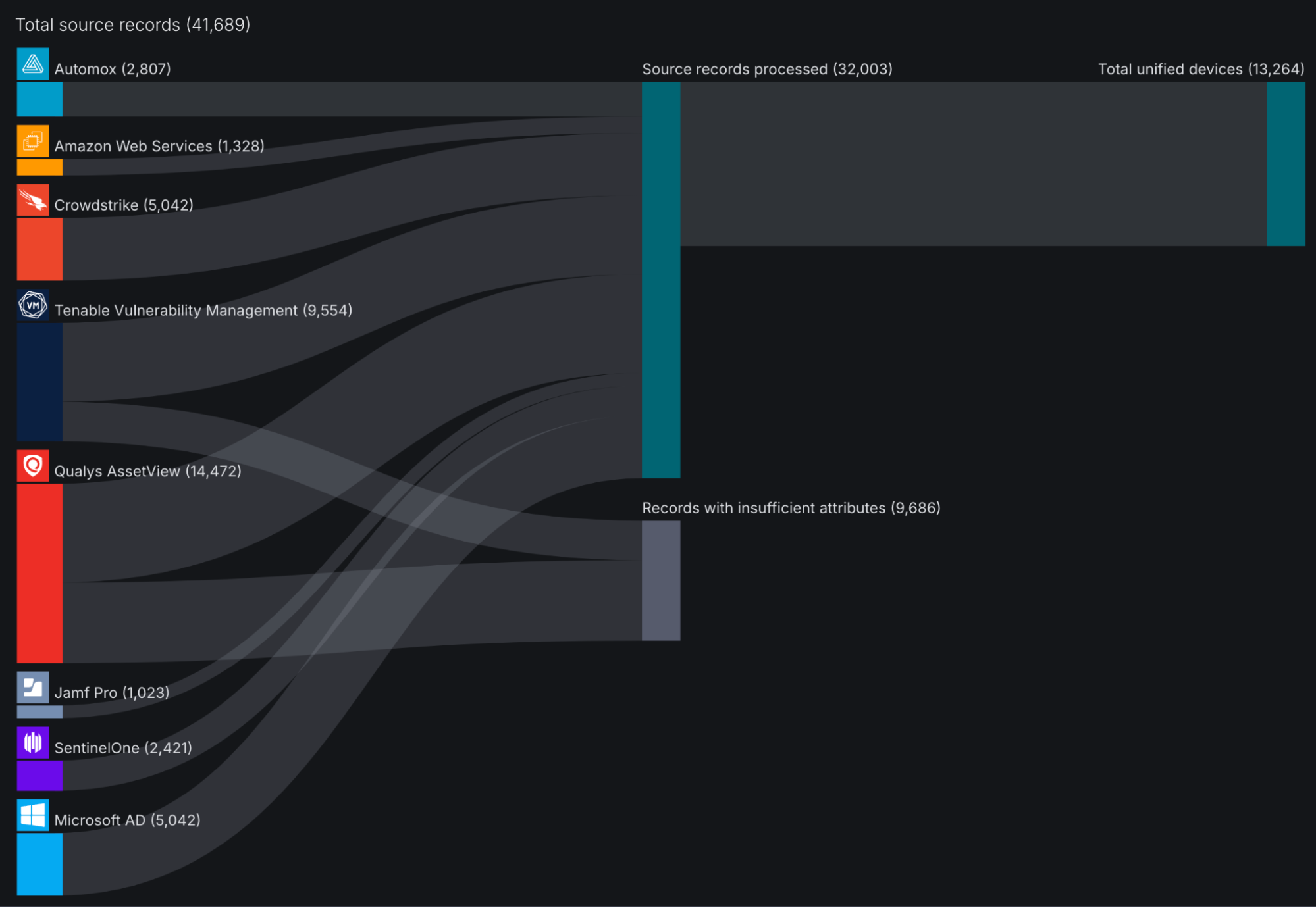
Sevco delivers a comprehensive inventory through:
- Aggregation and Deduplication: Sevco integrates with 1000s of existing security and IT tools via API to automatically ingest, aggregate, and deduplicate assets. The inventory Sevco delivers is live, meaning we’re pulling source data and running it through our correlation engine (Sevco’s proprietary data models) in real-time to ensure you always have an accurate picture of the entire attack surface.
We’ve named the inventory Sevco delivers the Security Inventory, because it goes beyond traditional constructs of an asset inventory.
|
Security Inventory |
Typical Inventory |
|
Multi-source aggregation |
Single source |
|
Live operational view |
Administrative |
|
Real-time and continuous |
Infrequent updates |
|
Rich indexing and searching |
Basic tables |
|
Maintains asset relationships |
Limited to no relationship mapping |
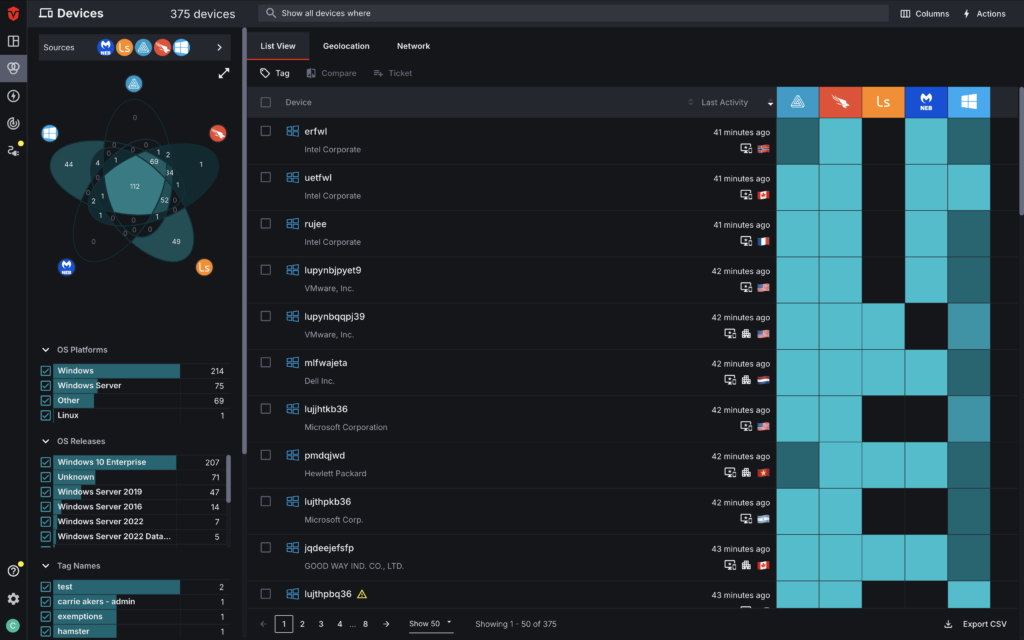
At Sevco, we identify six classes of assets:
- Devices – laptops, mobile phones, servers, etc.
- Identities – users, roles, and groups
- Software – applications hosted on assets
- Vulnerabilities and Exposures – more than just CVEs, we look at misconfigurations and controls coverage gaps, CSPM vulnerabilities, ASPM vulnerabilities, and traditional software vulnerabilities
- Cloud Assets – VMs, databases, storage buckets, etc.
- Security Controls Coverage – presence and state of critical controls
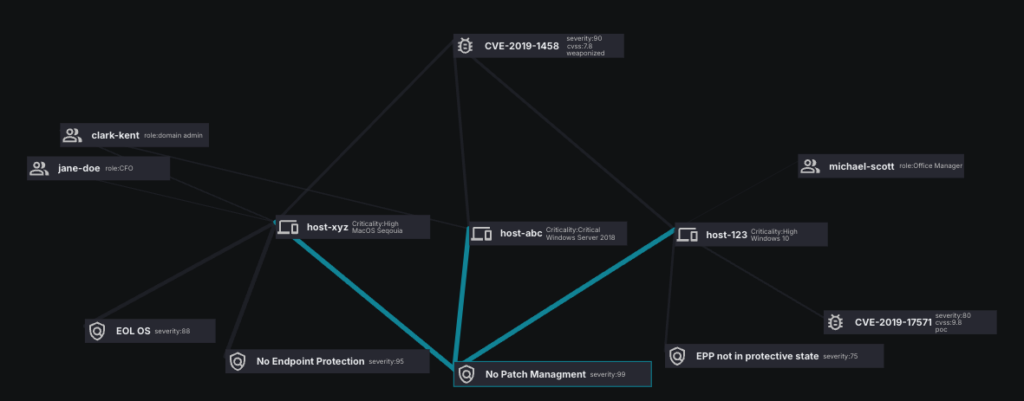
After creating a comprehensive inventory of all six asset classes, we correlate and deduplicate all of the data from the disparate sources to create an interconnected view. Think of a web that links devices to their users and vulnerabilities (and more) – at scale across your environment. Every relationship, perfectly mapped and maintained, automatically. This is the Asset Graph.
- Asset Graph: Relational mapping of the assets that make up the entire attack surface enables holistic visibility and informed decision-making.
- For example, Sevco can show you a critical production server tied to a domain admin user with a misconfigured EDR agent that has a critical, weaponized CVE that is unpatched.
Exposre Management (CTEM Discovery + Prioritization + Validation)
Discovery of Exposures and Vulnerabilities
Sevco identifies vulnerabilities beyond traditional CVEs, consolidating insights from:
- Vulnerabilities and Misconfigurations: This one is new for the industry, but we believe that misconfigured and missing security controls need to be identified and prioritized for remediation—just like CVEs. So, we coined our own term, CAASM Vulnerabilities. Within Sevco, you can see all the devices that are mis / missing configurations e.g. missing EDR or Patch Management agents.
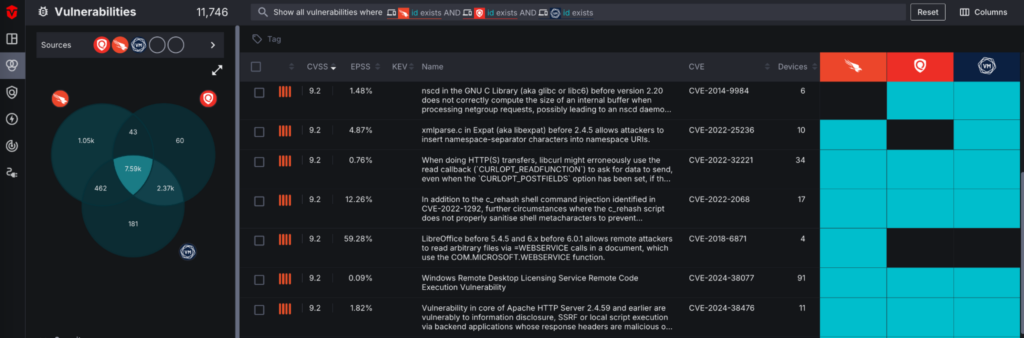
- Software Vulnerabilities (CVEs): Similar to the Security Inventory, we ingest, aggregate, and deduplicate CVE findings from multiple sources. The unique list of reported CVEs hold their own page within the Sevco platform, and can be prioritized for remediation individually (within this page), or holistically with other types of vulnerabilities.
- Cloud Security Posture Management (CSPM ) and Application Security Posture Management (ASPM) Vulnerabilities: As modern enterprises continue to migrate to the cloud, and the number of born in the cloud companies grow, so does the requirement for CSPM and ASPM vulnerability management. Like CAASM and CVE vulnerabilities, CSPM and ASPM vulnerabilities are ingested from specific CSPM / ASPM vendors, and hold their own space within the platform. Teams can identify, prioritize, and take action on misconfigurations, insecure APIs, access management issues, etc.
Prioritization of Exposures and Vulnerabilities
We believe that vulnerability prioritization is specific to every organization. While tools like CVSS are helpful in managing CVEs, many organizations need additional layers of context to effectively prioritize. Sevco goes beyond simplistic severity scores to provide nuanced, context-aware prioritization:
- Severity: a measure of how much a security vulnerability could impact a system or application. Sevco leverages industry standard frameworks to support prioritization based on vulnerability severity (e.g. CVSS, CISA Kev, EPSS).
- Exploit Likelihood: the probability that a discovered vulnerability will be actively exploited by a malicious actor. Sevco’s native exploit intelligence incorporates real-world data on exploits observed in the wild (e.g. exploit maturity, threat actor information, and patch availability). Learn more about exploit intelligence in Sevco’s platform.
- Business Context: Bespoke business information needs to be considered in prioritization. Sevco’s deep intelligence of all assets (specifically devices and users) create custom levels of prioritization – think asset criticality, asset ownership, etc.
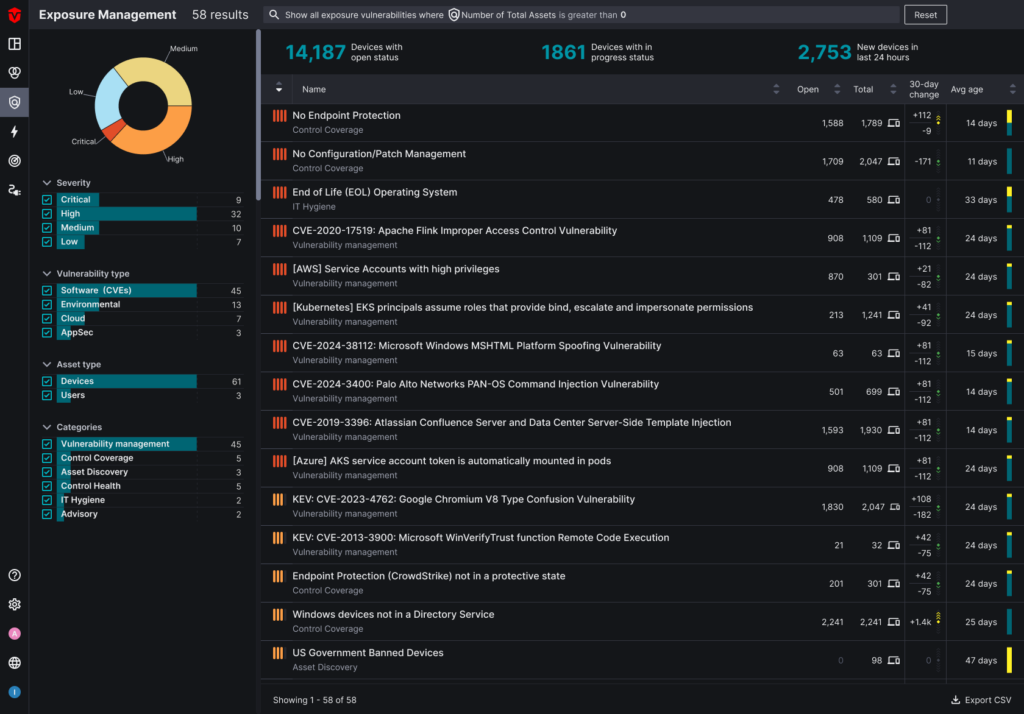
- Normalized Risk Quantification: Sevco normalizes risk scoring across the different types of vulnerabilities (CAASM, CVE, CSPM, and ASPM), enabling holistic prioritization of critical risk across the attack surface. Gone are the days of siloed prioritization.
See the power and flexibility of vulnerability prioritization with Sevco:
Validation of Exploitability
Layering the internal context and relevant external information is critical to having the right prioritization. Sevco’s intelligence enables customers to validate if an exposure or vulnerability has a proper chance of exploitation, ensuring that prioritized exposures represent true risks. Key capabilities include:
- Control Validation: Verifies the presence and state of mitigating security controls that could prevent exploits.
- Threat Intelligence: Intelligence on the tactics, techniques, and procedures bad actors are leveraging to execute malicious activities. And, leveraging the intelligence to determine if assets are vulnerable to the TTPs.
- External Visibility: Shows whether assets are external-facing and can be reached via the internet by bad actors.
Remediation (CTEM Mobilization)
Remediation and risk reduction are not solely the responsibility of the Security team – it is an organization-wide effort that requires orchestration between Security, IT, and the business. Sevco helps align and mobilize these teams by providing the details data they can use to address exposures and proactively harden the security posture of the organization:
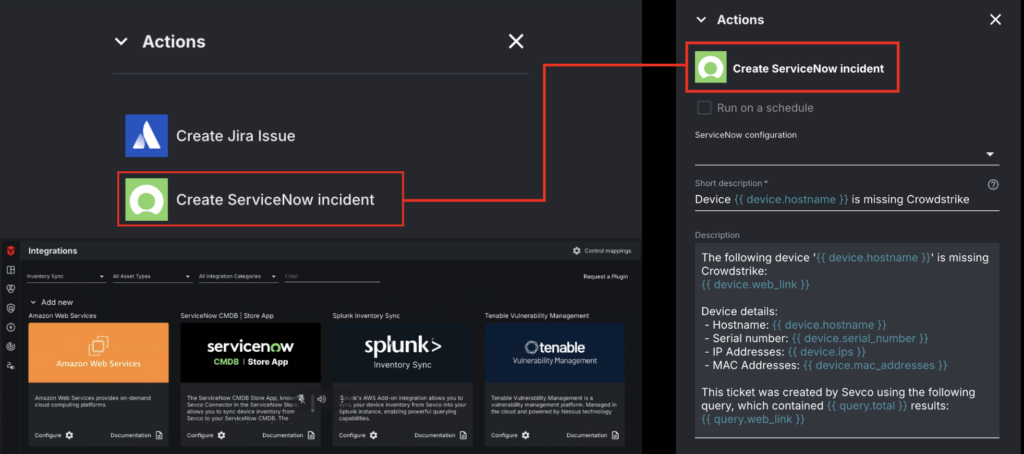
- Action Center: Taking Sevco data to kick off remediation efforts. Action Center automates workflows through bidirectional integrations with ITSM, CMDB, and SIEM tools. Whether it’s notifications in email or slack, ticket creation, or data enrichment, Sevco can facilitate the remediation process. And, the live Security Inventory can automatically verify when risk has been resolved. A complete feedback loop.
- Exposure Management Dashboard: After normalizing risk across different classes of vulnerabilities (CAASM, CVE, CSPM, ASPM), we prioritize the critical vulnerabilities in an Exposure Management dashboard. This page is both a way to review the biggest risks to the organization, but also to monitor their resolution, and report on key health metrics related to vulnerability and patch management.
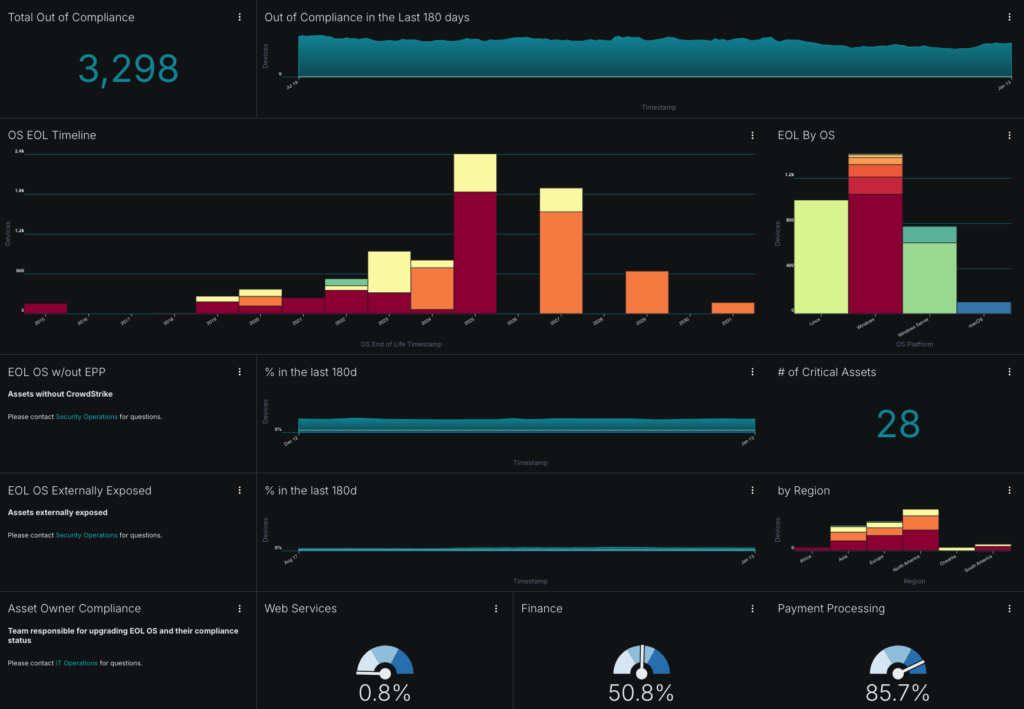
- Custom Reporting: Like our philosophy on prioritization, we believe that reporting often requires customization based on organizational needs. As such, we’ve developed flexible dashboards and reports that allow for tracking of bespoke initiatives.
Sevco Can Help
Bad data leads to bad decisions. A single missing asset or vulnerability can compromise the entire risk assessment. Siloed and inconsistent datasets lead to inefficient and ineffective exposure management and risk mitigation.
By centralizing the assets and intelligence teams require to find, prioritize, and remediate vulnerabilities, the Sevco Exposure Assessment Platform becomes mission control for security teams, addressing these challenges head-on by empowering organizations to:
- Gain full visibility into assets and associated vulnerabilities
- Prioritize and validate risks based on context
- Mobilize remediation efforts effectively and collaboratively
See Sevco in Action: Request a demo today to see how Sevco can transform your approach to exposure management.
